Research
Explore in-depth research on the latest cybersecurity threats, trends, and defense strategies. Get insights from Microsoft that’ll help you better understand and respond to today’s challenges.
Refine results
Topic
Products and services
Publish date
-
To help counter malware, we are releasing a new feature in Office 2016 that blocks macros from loading in certain high-risk scenarios.
-
Keeping browsing experience in users’ hands
Our evaluation criteria describe the characteristics and behavior of malware and potentially unwanted applications and guide the proper identification of threats. -
Microsoft updates Trusted Root Certificate Program to reinforce trust in the Internet
At Microsoft, we are continuously working to deliver on our commitment to the security of our customers and their ecosystems. -
Microsoft Security Intelligence Report: Strontium
The Microsoft Security Intelligence Report (SIR) provides a regular snapshot of the current threat landscape, using data from more than 600 million computers worldwide. -
Understanding type confusion vulnerabilities: CVE-2015-0336
In March 2014, we observed a patched Adobe Flash vulnerability (CVE-2015-0336) being exploited in the wild. -
Cleaning up misleading advertisements
Microsoft is committed to protecting our customers and their Windows experience. -
Your Browser is (not) Locked
Most ransomware has a binary file that needs to be executed before it can infect your PC. -
Microsoft cloud protection
(Note: Read about Windows Defender Antivirus cloud protection service in this blog entry: Windows Defender Antivirus cloud protection service: Advanced real-time defense against never-before-seen malware. -
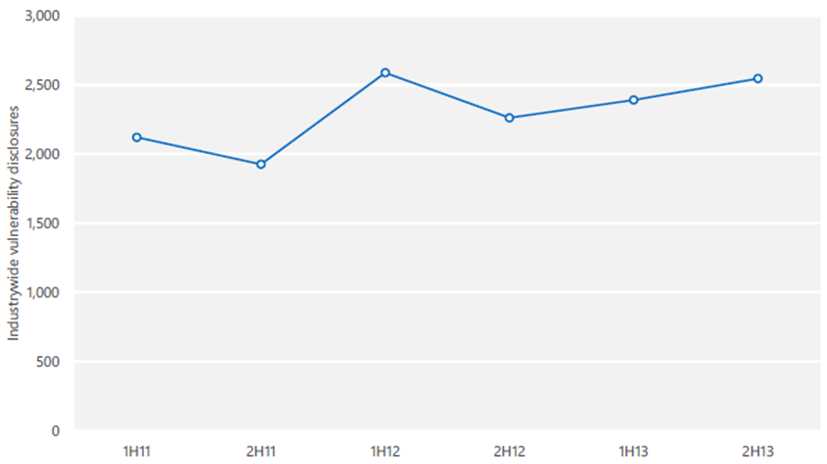
Industry Vulnerability Disclosures Trending Up
A vulnerability disclosure, as the term is used in the <a href=”http://www.
-
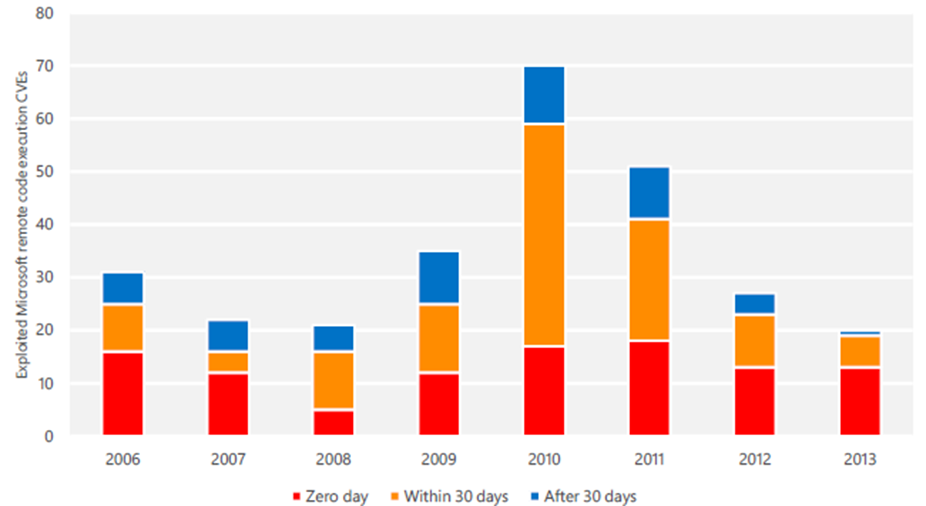
When Vulnerabilities are Exploited: the Timing of First Known Exploits for Remote Code Execution Vulnerabilities
One of the questions I get asked from time to time is about the days of risk between the time that a vulnerability is disclosed and when we first see active exploitation of it; i.
-

New Microsoft Threat Modeling Tool 2014 Now Available
Today we’re announcing the release of the <a href=”http://download.